Coreon offers three log-in methods to access a repository as an authenticated user:
- Coreon Credentials: This is Coreon’s own user management module to store user name/password combinations.
- Single Sign-On: A repository can be configured to federate the authentication mechanism to an organisation’s so-called Identity Provider. If configured, you log in to the repository via the credentials you use when logging in to your organisation’s intranet.
- API Key: A simple string token that you submit, and the focus of this blog post! Let’s look in more detail at how this works…
API Keys are particularly good for software developers integrating Coreon as a backbone service into other solutions. Such a key – a cryptical string – is a comfortable and very easy method to connect two applications.
How do Coreon API keys behave?
- A key is bound against a valid repository user. Thus, when authenticating via such a key, the granted rights (what you can see, what you can do) in the repository are identical to the rights of the user.
- A key can have a time range when it is valid (“from date to date”). This can be helpful when you want to hand out an API key to a partner organisation and you want to ensure that the key expires after a given point in time, when a project activity is planned to come to an end.
- API keys are less foreseen as something to be typed into a Login dialog box. Their purpose is rather to be embedded directly within other software applications.
How to generate an API key?
- Log in to the Coreon dashboard as the user you want to generate the key for.
- Select the repository (as mentioned, a key is bound against a user of a repository).
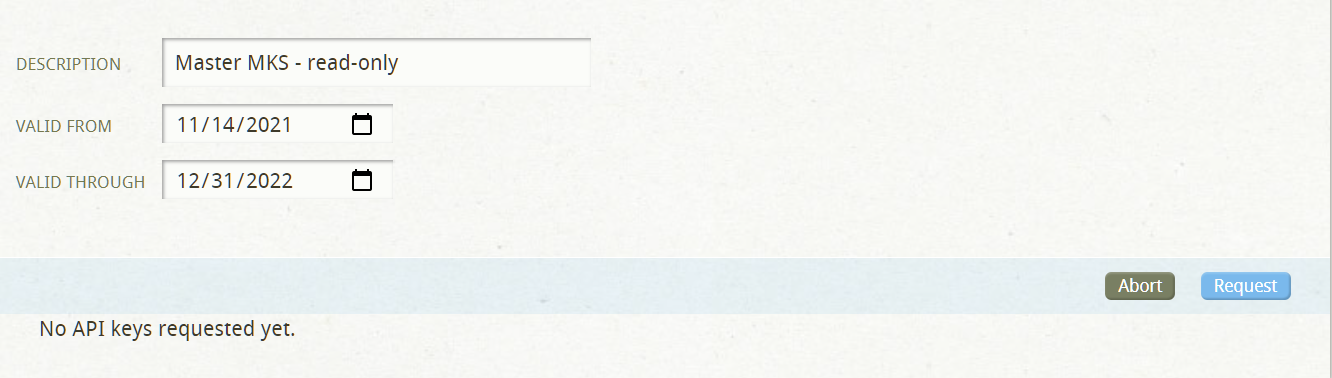
- Click API Keys / Request API Key button:
- Provide a short description (mandatory).
- Provide validity start and end dates (optional).
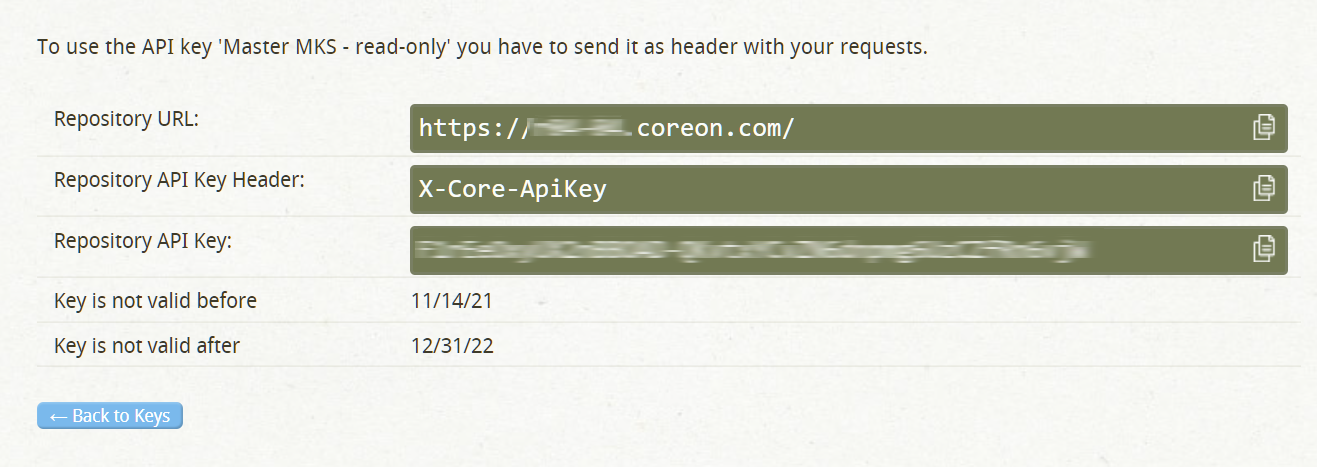
- Click Request to get the key – the key is generated and its properties are shown:
How to use an API key?
Usually API keys are embedded into other software solutions, directly accessing a repository via the Coreon API or its SPARQL endpoints. As a developer you would include the API Key in the request header when accessing the repository.
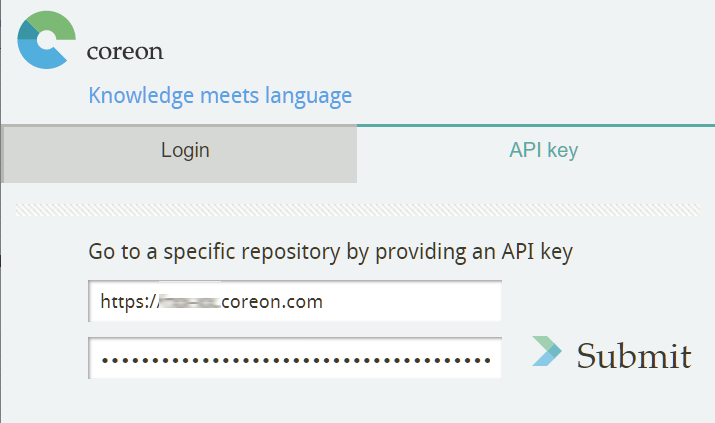
Some applications may also allow to directly type in an API key to authenticate, namely as an alternative to the other authentication methods. For instance, in Coreon’s browser extension to Google Chrome/Microsoft Edge, you can use an API key to connect. To do so you would provide the repository URI together with the key token to access the Multilingual Knowledge System:
Notes
When you want to change the repository, you’d need to use/submit another API key. This is because an API key is always bound to a user in one given repository.
API keys can be changed. When you would like to change the validity of a key, go to the Coreon dashboard, select the key and modify its start/end dates. The token itself does not change. Thus the key remains functional, only its “meaning” has changed.
Are you a software developer and want to know more? Please contact us – the API keys are documented as part of the Coreon API specification.